- Share Microsoft issues ‘highly unusual’ Windows XP patch to prevent massive ransomware attack. Share tweet Linkedin Reddit Pocket Flipboard Email. UK hospitals, Telefonica, FedEx.
- That security bulletin only included fixes for Windows Vista, Windows 7, Windows 8.1, Windows 10, Windows Server 2008, Windows Server 2012, and Windows Server 2016.
Wannacry Microsoft Patch Windows 7
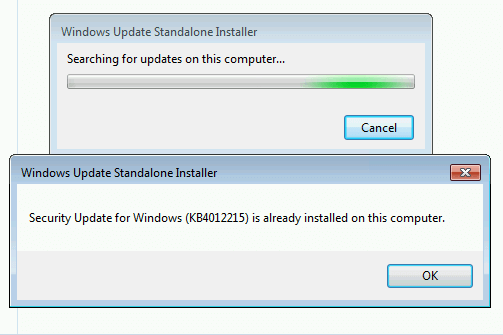
You should bear in mind that this security patch which Microsoft has released for Windows Vista/XP/Server 2003/2008, is a one-off patch Microsoft produced in response to the sudden, drastic impact.
Users of old Windows systems can now download a patch to protect them from this week’s massive ransomware attack.
In a rare step, Microsoft published a patch for Windows XP, Windows Server 2003 and Windows 8—all of them operating systems for which it no longer provides mainstream support.
Users can download and find more information about the patches in Microsoft’s blog post about Friday’s attack from the WannaCry ransomware.
The ransomware, which has spread globally, has been infecting computers by exploiting a Windows vulnerability involving the Server Message Block protocol, a file-sharing feature.
Computers infected with WannaCry will have their data encrypted, and display a ransom note demanding $300 or $600 in bitcoin to free the files.
Win 7 Wanna Cry Patch Download Full
Fortunately, Windows 10 customers were not targeted in Friday’s attack. In March, Microsoft patched the vulnerability that the ransomware exploits—but only for newer Windows systems. That’s left older Windows machines, or those users who failed to patch newer machines, vulnerable to Friday’s attack.

Researchers originally believed the ransomware was spread through attachments in email phishing campaigns. That no longer appears to be the case.
Once a vulnerable PC becomes infected, the computer will attempt to spread to other machines over the local network as well as over the internet. The ransomware will specifically scan for unpatched machines that have the Server Message Block vulnerability exposed.
Businesses can prevent this by disabling the Server Message Block protocol in vulnerable PCs. They can also use a firewall to block unrecognized internet traffic from accessing the networking ports the Server Message Block uses.
Fortunately, Friday’s ransomware attack may have been contained. A security researcher who goes by the name MalwareTech has activated a sort of kill-switch in WannaCry that stops it from spreading.
As a result, over 100,000 new infections were prevented, according to U.K.’s National Cyber Security Centre. But experts also warn that WannaCry’s developers may be working on other versions that won’t be easy to disable.
“It’s very important everyone understands that all they (the hackers) need to do is change some code and start again. Patch your systems now!” MalwareTech tweeted.
Unfortunately, the kill-switch’s activation will provide no relief to existing victims. The ransomware will persist on systems already infected.
Friday’s ransomware attack appears to have spread mainly in Europe and Asia, with Russia among those nations hardest hit, according to security researchers.
Security experts are advising victims to wait before paying the ransom. It’s possible that researchers will develop a free solution that can remove the infection.
This story was updated at 11:33 AM on May 15 to add and correct misinformation from researchers.